Insurance
Digitally verified virtual inspections
Control fraud, reduce operative costs and introduce reliable traceability with Inkan’s workflow builder. Powered by photo, video and documentation verification technology.
Inkan Platform
Reduce costs, prevent fraud and improve traceability
Streamline policy and claim processing and rapidly collect 100% authenticated images and documentation to reduce risk and increase operational efficiency, through Inkan’s technology based on cybersecurity, blockchain and artificial intelligence.
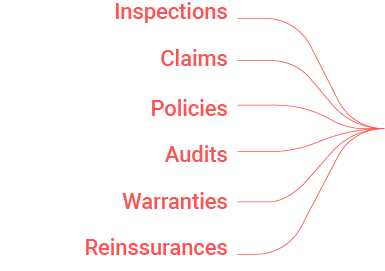

Pipeline
Streamline inspections anywhere, anytime
Inkan is a platform that helps you evolve from manual policy and claim processes into automated digital workflows, easily sending requests and instantly reviewing trustworthy photos, videos and data from your customers, suppliers and partners.
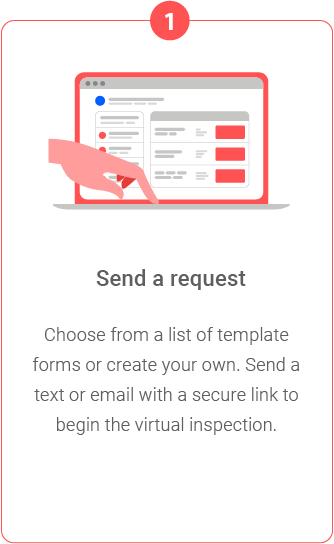
How Inkan Works
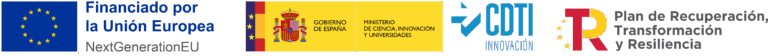
Mobile App
Transform your images into proof
with Inkan's App
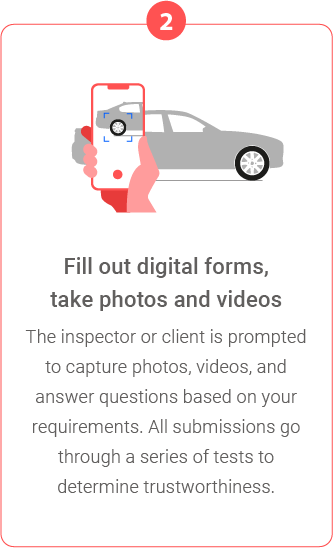
Ensured authenticity
Inkan’s camera redefines the expression “capturing the moment”, by associating the images it produces with the exact place, time, device and user. Thanks to blockchain technology and cybersecurity, data is protected and sealed by anti-tampering layers. Anyone can easily check an image’s authenticity and source information. We know for certain if it has been altered in any way.
Fast processing, fraud prevention
and traceability
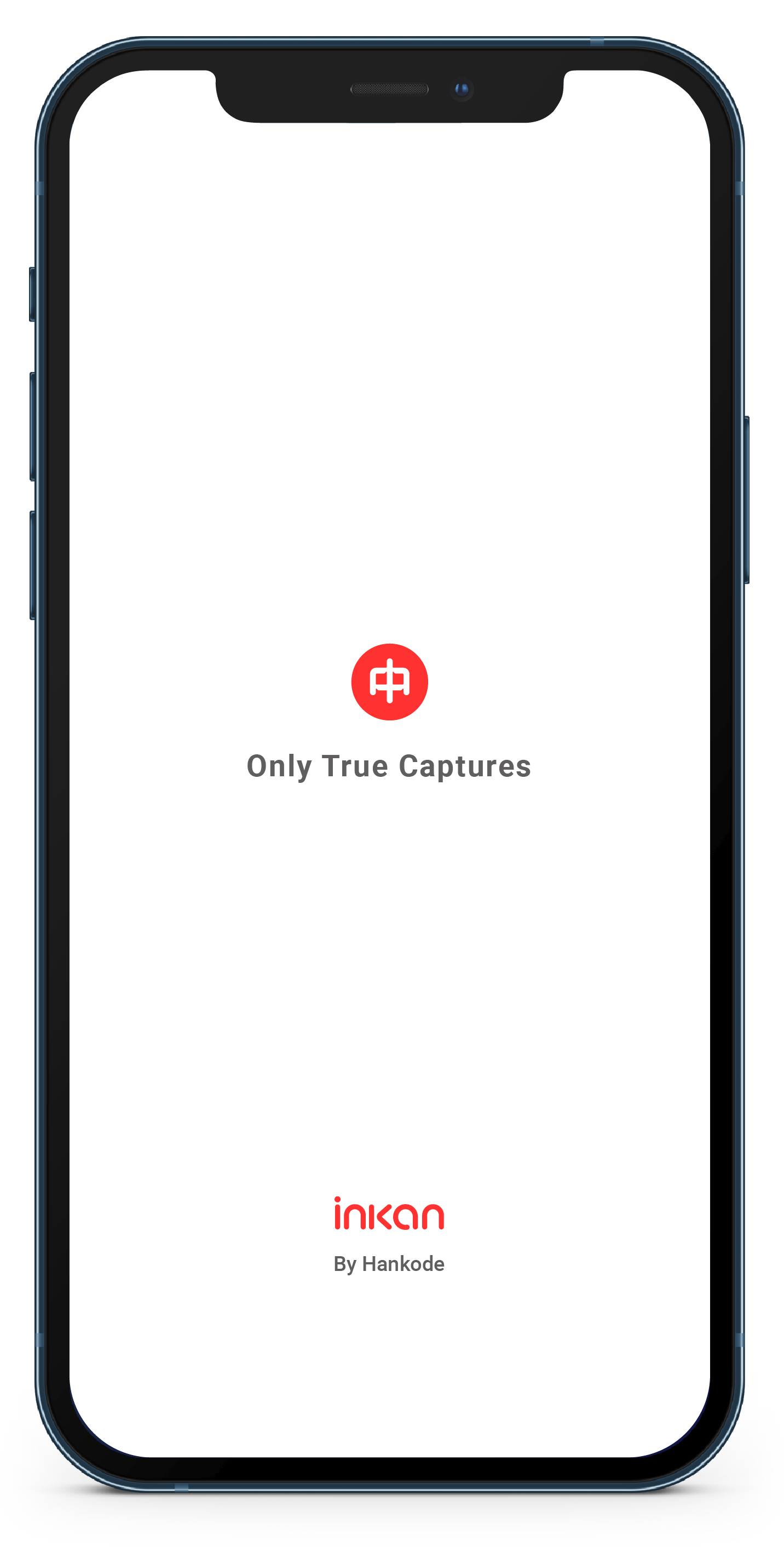
Inkan Platform
Streamlined inspections anywhere, anytime
Tasks Management
Create customizable tasks for inspections, claims, policies, QC and other workflows based on digitally signed, verified and certified images, forms and documentation.
Workflows builder
Inkan is a flexible tool that adapts to specific workflows with a common principle: safe channels for data ingestion, tamper-proof database, fraud prevention and traceability.
Customizable forms
Use a template or create your own form through Inkan’s intuitive interface. Simplify inspections in situ with easy to use forms, task and user management, all in the cloud.
Report Generation
Automatic report generation that will save you time and money. Build your pdf report templates, with accurate and trustworthy traceability for your images, forms and documentation.
Cost reduction based on trusted information

Avoid costly site inspections with Inkan's remote workflows based on high trust data and image collection.
With our digital inspection platform, we offer a fast and convenient way to receive verified and reliable images, videos and information directly from your customers, suppliers and partners.
Revolutionize your site inspections


Fraud Detection with AI
Automated trust for photos, videos and documentation
Inkan Platform validates the authenticity of uploaded photos and videos provided by any source. Using our AI technology, we can trust what we see. Our deep learning proprietary algorithms based on convolutional neural networks are able to detect:

Look how Inkan Platform transforms images into proof
Cost Reduction
You can remotely request trusted inspection images to your customers, partners and suppliers
Fraud Prevention
Reduce and mitigate risk by preventing fraud with images even before it happens
Traceability
Place, time, device and user provenance information is sealed and authenticated building a solid data traceability workflow
Cost Reduction
You can remotely request trusted inspection images to your customers, partners and suppliers
Fraud Prevention
Reduce and mitigate risk by preventing fraud with images even before it happens
Traceability
Place, time, device and user provenance information is sealed and authenticated building a solid data traceability workflow
Don't wait any longer, create safe channels for your information
Reduce costs, improve your brand perception, gain a competitive advantage by integrating novel technologies and services
© 2025, Inkan, All Rights Reserved, Mimesis Contents, S.L.